Darren Samuelsohn reports in Politico that a “survey of battleground state election officials paints a troubling picture” of how “woefully unprepared” they are for an election day cyber attack.
From Politico:
While states have spent years thinking about and planning for other types of crisis that can mess with voting — from hurricanes to power blackouts and terrorist attacks — they’ve been slow and ill staffed to develop contingency plans responsive to a hack attack that would adequately protect their systems in time for the 2016 presidential election.
…
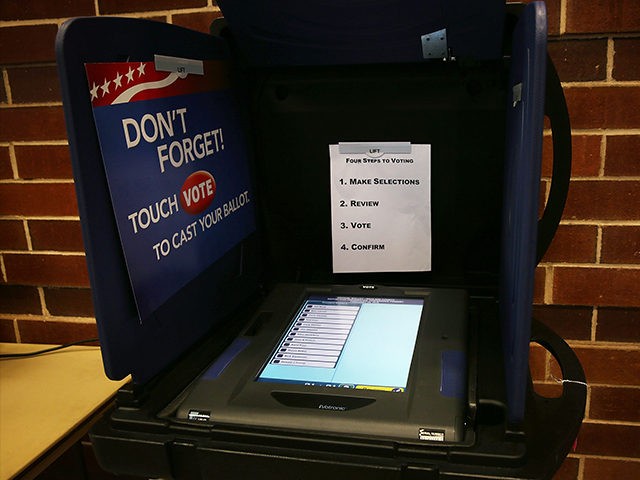
A dozen battleground state officials surveyed by POLITICO insist the voting systems themselves are safe, as nearly all parts of the balloting process take place in a secure, offline environment. But they also repeatedly acknowledged there are limits to what they can control, and they recognize they face legitimate challenges from cyber intrusions to the myriad adjacent parts that go into an election, including online registration records and publicizing vote tallies.
While any manipulation of a state’s official election results is seen as unlikely, there’s little denying that an Internet disruption or hack could cause significant confusion and chaos on Election Day, a dark conclusion to an ugly election plagued by accusations of Russian cyber espionage and evidence-less allegations of vote tampering and rigging.
Just last week, hackers temporarily froze a sizable chunk of the internet, a worst-case scenario that would cause serious problems around the country if duplicated on Nov. 8 — the day more than 100 million Americans are going to the polls.
…
Federal agencies have also been scrambling since the summer to help state and local officials prepare emergency plans for the 2016 election, including via an added emphasis on cyber risks. Breaches earlier this summer to the voter registration databases in Illinois and Arizona prompted the FBI to issue a nationwide alert to the other states. The Homeland Security Department has also gotten requests from 42 states seeking help shoring up their cyber hygiene practices and assessing their online vulnerabilities.
Read the rest here.

COMMENTS
Please let us know if you're having issues with commenting.