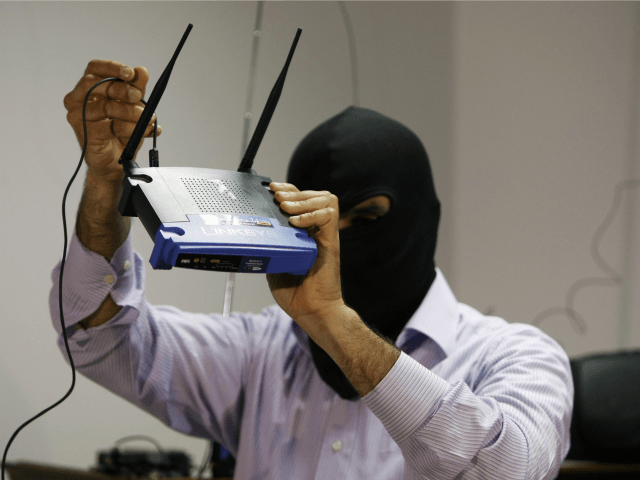
WikiLeaks released the latest exploit titled ‘Cherry Blossom’ from their CIA Vault 7 series last week. The release details methods the CIA has used to take control of wireless Internet routers to breach their target’s systems.
WikiLeaks’ latest leak from their CIA Vault 7 series reportedly outlines a tool used by the CIA to monitor and perform software exploits on specific targets. WikiLeaks claims that this tool was developed and implemented with the help of the US nonprofit Stanford Research Institute (SRI International).
“CherryBlossom provides a means of monitoring the Internet activity of and performing software exploits on Targets of interest.” reads the WikiLeaks leak page, “In particular, CherryBlossom is focused on compromising wireless networking devices, such as wireless routers and access points (APs), to achieve these goals. Such Wi-Fi devices are commonly used as part of the Internet infrastructure in private homes, public spaces (bars, hotels or airports), small and medium sized companies as well as enterprise offices.”
The description continues to say, “Therefore these devices are the ideal spot for “Man-In-The-Middle” attacks, as they can easily monitor, control and manipulate the Internet traffic of connected users. By altering the data stream between the user and Internet services, the infected device can inject malicious content into the stream to exploit vulnerabilities in applications or the operating system on the computer of the targeted user.”
These Wi-Fi devices are reportedly compromised by installing a custom CherryBlossom firmware on them via wireless connection, this means that physical access to the device is not needed to install the firmware. Once the firmware is installed, the device becomes what is called a FlyTrap which acts as a beacon, transferring info to a Command & Control server referred to as a CherryTree. The info transferred to the CherryTree contains device status and information which is logged to a database by the CherryTree.
WikiLeaks outlined how the CherryTree then uses this information saying, “In response to this information, the CherryTree sends a Mission with operator-defined tasking. An operator can use CherryWeb, a browser-based user interface to view Flytrap status and security info, plan Mission tasking, view Mission-related data, and perform system administration tasks.”
Read the full WikiLeaks release here.
Lucas Nolan is a reporter for Breitbart News covering issues of free speech and online censorship. Follow him on Twitter @LucasNolan_ or email him at lnolan@breitbart.com

COMMENTS
Please let us know if you're having issues with commenting.