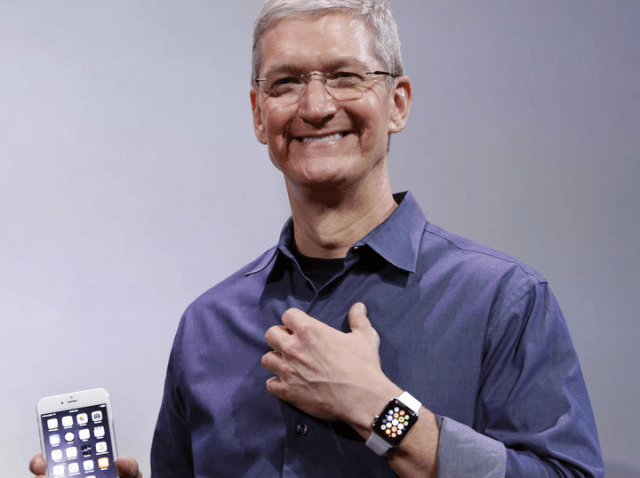
CEO Tim Cook says the court order won by the FBI is the “software equivalent of cancer.”
The FBI won the federal court order from California Magistrate Judge Sheri Pym, who directed Apple to write an app that will open the iPhone used by San Bernardino terrorist Syed Farook before he and his wife murdered 14 Americans.
Apple Inc. (AAPL:NASDAQ) is currently in a war with the FBI and public opinion. The company claims the FBI wants Apple to build a special version of iOS that would weaken the device’s security and install it on the device.
Cook has cast himself as a warrior on the side of justice, but he or another Apple executive could end up with a contempt order from a federal judge on Feb. 26 and end up spending a few days behind bars.
Apple probably has achieved a marginal win with members of the tech community that believe fighting the FBI and the Justice Department’s efforts to force the Apple to write an app to unlock the mobile device of a known murderous terrorist’s iPhone is a sign of Cook’s respect for privacy.
But the reputation of Apple’s brand may suffer a loss with consumers, since a Pew poll indicates that the majority of Americans and a plurality of every single age demographic in the U.S. believe Apple should follow a federal court order to assist the FBI in unlocking the iPhone.
The legal case pits issues of national security against constitutional rights of privacy. The standoff with the FBI brings to a boil the simmering battle between law enforcement and Silicon Valley over encryption technology that can permanently scramble data to prevent unauthorized readers from seeing it.
The Justice Department’s Feb. 19 Motion to Compel argued that a court order would not create a “backdoor” that could contribute to a general decrypting of any of Apple’s phones or serve as carte blanche for government to compromise the security of personal information.
But in an interview, Cook told ABC’s David Muir that his fear is that enabling backdoor access to the iPhone, which he described as “the software equivalent of cancer,” sets a dangerous precedent that would risk both the “privacy” and “public safety” of over 700 million iPhone uses in 130 nations around the globe.
Cook highlighted that Apple clearly stated outlined its opposition to the court order in a letter to customers and an internal note to staff released to the general public.
FBI Director James Comey in Congressional Intelligence Committee testimony responded to Apple’s public relations campaign by stating:
“The Order requires Apple to assist the FBI with respect to this single iPhone used by Farook by providing the FBI with the opportunity to determine the passcode. The Order does not, as Apple’s public statement alleges, require Apple to create or provide a “back door” to every iPhone; it does not provide “hackers and criminals” access to iPhones; it does not require Apple to “hack [its] own users” or to its own phones.”
But Comey did concede for the first time that future judges will look to the FBI’s battle with Apple as a precedent for law enforcement access to locked or encrypted mobile devices. James Comey commented on Feb. 18 that the outcome of his battle with Apple will “guide how other courts handle similar requests.” The FBI Director three days later also said that the court decision will “set a precedent”.
In a last-ditch effort, Apple filed a 35-page brief on Feb. 25, titled, “Motion to Vacate the Order Compelling Apple Inc. to Assist Agents in Search, and Opposition to the Government’s Motion to Compel Assistance.” Apple argued the government’s reliance on the “All Writs Act,” which traces its roots to the Judiciary Act of 1789, cannot serve as a basis to “conscript” Apple to make an app to enable the government to hack its phones.
The ‘ars technical blog’ broke a story that in November 2014, the Oakland Division of the U.S. Attorney’s Office used the All Writs Act to try to leverage Apple Inc. into writing an app to extract data from a locked iPhone 5C, as part of a criminal case.
In that case, Magistrate Judge Kandis Westmore ordered that Apple to “provide reasonable technical assistance to enable law enforcement agents to obtain access to unencrypted data,” but she did not specifically mention the All Writs Act as a precedent.
But she did add, “It is further ordered that, to the extent that data on the iOS device is encrypted, Apple may provide a copy of the encrypted data to law enforcement but Apple is not required to attempt to decrypt, or otherwise enable law enforcement’s attempts to access any encrypted data.”
The desired iOS app would allow the FBI to use “brute force” by trying millions times to crack the device’s pin code without delay or the device erasing itself to open the iPhone memory. A federal court has been given a Feb. 26 deadline for Apple to comply with its order.
Although Tim Cook’s outspokenness could get him sent to the slammer, most legal experts believe if Apple losses the Motion to Compel, it will be allowed to appeal.

COMMENTS
Please let us know if you're having issues with commenting.