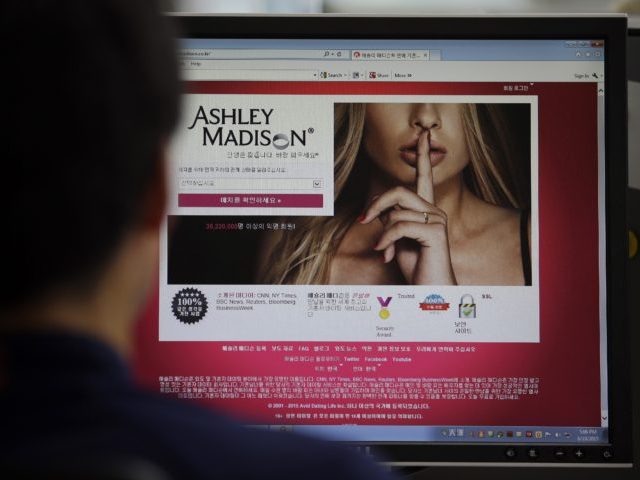
The latest users of the infamous adultery website Ashley Madison to have been exposed are European Union bureaucrats. The hack of the website’s membership list reveals 13 officials used work email addresses to register their interest, raising serious international security issues.
To some, 13 people out of a list of 36 million Ashley Madison subscribers whose personal data have been published by ‘The Impact Team’ may not seem a great deal. However, EurActiv (who revealed the officials’ involvement) points out that it does raise serious questions over potential security breaches, both through blackmail and the private information revealed in the hack itself.
The stolen data, still available online, includes personal information such as sexual orientation and what the user is looking for in a sexual partner. That sort of information can easily be used by terrorist groups to blackmail EU officials. From a security perspective the publication of banking details and private addresses is also very problematic.
In addition, the Ashley Madison hack reveals users’ questions and answers used to recover passwords, and even the encrypted passwords themselves. Euractiv points out that data can be used to change passwords, access accounts and if, as is often the case, a subscriber uses the same secret questions and answers for multiple websites, could lead to further security breaches.
In total EurActiv found eight Commission officials – including one Head of Unit – using official “@ec.europa.eu” email addresses to sign up to the website. Seduced by the slogan ‘Life is short. Have an affair’, three European Parliament workers, including a major political group’s policy advisor, used their official “europarl.europa.eu” addresses.
Furthermore, one signed up from the from the European External Action Service (the EU’s foreign ministry and diplomatic corps), another from the EU’s financial regulator, the European Securities and Markets Authority, and perhaps most chillingly given its role in the Common Security and Defence Policy, one from the EUFOR rapid reaction force.
As others have said in their own defence, inclusion on the list does not mean individuals ever conducted an affair (although one of them was listed as having paid $82 to the site) and some have claimed their details were stolen. However, the security issues go beyond the embarrassment of adulterous exposure.
Even though EurActiv declined to name officials involved, the combination of information now in the public domain and the partial information they published has made the risk all the more serious.

COMMENTS
Please let us know if you're having issues with commenting.