The search for perpetrators of last week’s massive cyberattack has begun. While President Obama said “we don’t have any idea who did that” in a talk-show appearance on Monday, Director of National Security James Clapper stated on Tuesday that preliminary evidence suggested it was not the work of a hostile foreign government.
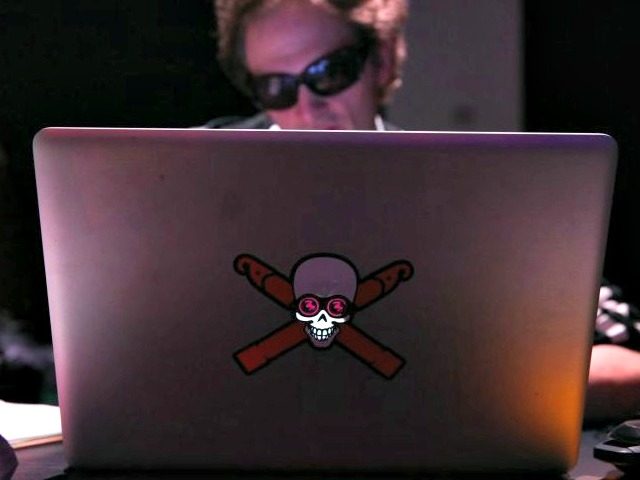
CNN reports the FBI and the U.K.’s Home Office are also involved in the investigation. The attack emanated from a huge number of Internet-enabled devices around the world, which had been corrupted with malware and turned into Denial-of-Service weapons, and targeted the New Hampshire-based Dyn corporation. Websites across the United States and Europe were disrupted by the temporary overload of Dyn’s servers.
The Department of Homeland Security is involved, with DHS Secretary Jeh Johnson promising a grand strategy for securing the Internet of Things within “the coming weeks.”
Of course, Dyn is also investigating the attack, in conjunction with its security providers, but TechRepublic points to a company statement that “we are unlikely to share all details of the attack and our mitigation efforts to preserve future defenses.” The general public probably should not expect regular updates from either the government or private investigators, until and unless solid evidence pointing to a likely suspect is compiled.
One of the problems with tracking down the perpetrators is that the malware employed in the attack was released into the public domain long ago – it’s like a gun found at a crime scene that can’t be traced through ballistics.
Fortune suggests blaming the manufacturers whose shoddy security standards allowed so many devices to be hijacked for the assault, warning they could very well be hijacked again, because the security flaws are all but impossible to correct. While we are at it, we can blame the government for failing to properly regulate the Internet of Things, and ourselves for leaving so many passwords set to the default value of “password”:
It’s a good bet these companies are scrambling to update their product lines in a way that requires users to change the passwords (widespread use of default passwords are the main reason the devices got hacked in the first place). But it’s not fair to lay the entire blame squarely on the companies. Part of the responsibility should also lie with lawmakers and regulators, who have failed to create a safety system to account for the Internet-of-Things era we are now living in.
Finally, it’s time for consumers to acknowledge they have a role in the attack too. By failing to secure the internet-connected devices, they are endangering not just themselves but the rest of the Internet as well. No one thinks it’s acceptable for consumers to be clueless when they operate products like automobiles or propane tanks – so why is it okay for them to be careless with routers and security cameras?
Some of this ire would seem misguided, since security experts have pointed out the compromised devices were not all penetrated with end-user passwords – back doors and passwords invisible to the consumer were also involved. A regulatory regime with the power to force consumers to change their passwords on every single Internet of Things device, and forces them to choose a password harder to crack than their cat’s name or wife’s birthday, would be formidable indeed.
Attorney Michael Zweiback told Fortune that lawsuits against IoT manufacturers are most likely on the way, along with investigation by the Federal Trade Commission and state attorneys general. Makes of these devices may be held liable for “dangerous products and deceptive marketing.”
Consumer class action lawsuits are also a possibility, although Zweiback noted the owners of devices used in the attack may have a difficult time establishing they were harmed by the botnet virus. Dyn, its customers, and users of the affected websites would have an easier time demonstrating harm. Dyn did not return a call from Fortune seeking comment on the possibility of lawsuits.
Heavy.com collected some theories about the identity of the attacks from around the Internet: it was intended to interfere with the WikiLeaks document drop; it was WikiLeaks looking for revenge against those who interfered with the document drop; or it was Russia firing a shot across the Obama Administration’s bow, after the Administration threatened cyber-warfare over the alleged Russian connection to WikiLeaks.
Included in the Heavy.com roundup was a more obscure theory that a group of anarchic hackers pulled off the attack for fun, and the true target was the major new video game “Battlefield 1.”
There has actually been a completely unverified claim of responsibility, but from a different group than the one Heavy.com mentioned: a collective called New World Hackers claims it struck at Dyn to demonstrate its capabilities, that the primary target was actually Twitter, and that its next target would be the Russian government.

COMMENTS
Please let us know if you're having issues with commenting.