Hackers penetrated the Friend Finder Network in October in one of the largest known personal data breach in history, with over 412 million accounts compromised.
The UK Guardian compares the breach to earlier milestones like the 2013 leak of 359 million users’ details from MySpace, or 33 million users of the Ashley Madison adultery website, and finds the scale of the Friend Finder hack exceeded only by the compromise of 500 million Yahoo accounts in 2014.
Among other properties, Friend Finder Networks includes the sex-hookup site Adult Friend Finder, which has 339 million accounts, and Penthouse.com, which has about 7 million users.
In a further uncomfortable complication for Friend Finder Networks, it doesn’t actually own Penthouse.com any more – the domain was sold to Penthouse Global Media last February. That means Friend Finder really shouldn’t have been in possession of a Penthouse.com user database for the hackers to raid. The hacked database also contained 16 million deleted accounts that were evidently never purged, which is similar to one of the complaints leveled against Ashley Madison after their hacking incident.
The Guardian reports the compromised accounts include “78,301 US military email addresses, 5,650 US government email addresses and over 96m Hotmail accounts.”
ZDnet is among those charging the hack was made possible by poor security practices at Friend Finder Networks, including the apparent refusal to swiftly address a security flaw discovered by a security researcher called “Revolver” (who denied having any involvement in the subsequent attack, although he did threaten to “leak everything” on his now-suspended Twitter account if the company tried to deny the security flaw he uncovered.)
Also, user passwords were reportedly stored in a relatively insecure manner in the database, making it too easy for the hackers to crack them.
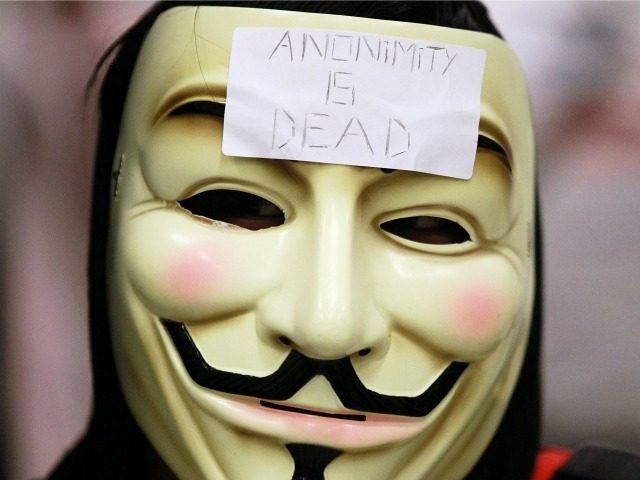
Friend Finder Networks has not yet officially admitted to the data breach; it was reported to the media by LeakedSource, a website that “specializes in bringing hacking incidents to the public eye.” They told Wired they were given the stolen Friend Finder data by an “underground source who wishes to stay anonymous.”
LeakedSource reported discovering that in almost 16 million incidences, email addresses in the lead Friend Finder database had been changed to include “@deleted1.com” at the end, which looks like a way of marking them ‘deleted” without actually erasing the data. “Uh oh,” was their pithy comment on this practice.
“Passwords were stored by Friend Finder Network either in plain visible format or SHA1 hashed (peppered),” the LeakedSource security report continued. “Neither method is considered secure by any stretch of the imagination and furthermore, the hashed passwords seem to have been changed to all lowercase before storage which made them far easier to attack but means the credentials will be slightly less useful for malicious hackers to abuse in the real world.”
LeakedSource thought this was especially negligent because Adult Friend Finder had already been hacked once before, in May 2015, and the login credentials of some 4 million users were among the items of information disclosed.
There’s also some reproach for Friend Finder users in the LeakedSource report, as they published a list of the passwords most commonly chosen by users, and it’s pretty depressing. The Number One password, chosen by over 900,000 users, was “123456.” The word “password” chugged in at #7 with 101,046 uses. Some of the other top-75 passwords were, shall we say, phrases that would be fairly easy to guess, if one was trying to crack a pornography website.
“This is attack on Adult Friend Finder is extremely similar to the breach it suffered last year. It appears to not only have been discovered once the stolen details were leaked online, but even details of users who believed they deleted their accounts have been stolen again. It’s clear that the organisation has failed to learn from its past mistakes and the result is 412 million victims that will be prime targets for blackmail, phishing attacks and other cyber fraud,” declared David Kennerly, director threat research at Webroot, as quoted by the Guardian.
“FriendFinder’s data debacle represents nearly 13 times as many accounts as the Ashley Madison breach. FriendFinder users can only hope that the leaked data remains relatively hidden. In the Ashley Madison case, by contrast, data was widely circulated and even made searchable on a highly trafficked website,” writes Wired.
LeakedSource has said it will not make the stolen data available to the public in searchable format, but pointed out other sources are likely to obtain the data and post it online.
COMMENTS
Please let us know if you're having issues with commenting.