Recently declassified NSA documents show a worrying lack of attention to digital security at the National Security Agency.
The declassified document obtained under a Freedom Of Information Act (FOIA) request by the New York Times, outlines a number of security measures taken by the NSA to secure their digital documents and systems. According to the report, the NSA regularly left physical server stacks completely unsecured and open to tampering, did not use two-factor authentication in many of their digital systems and did not use access control lists to verify which users should have access to sensitive information.
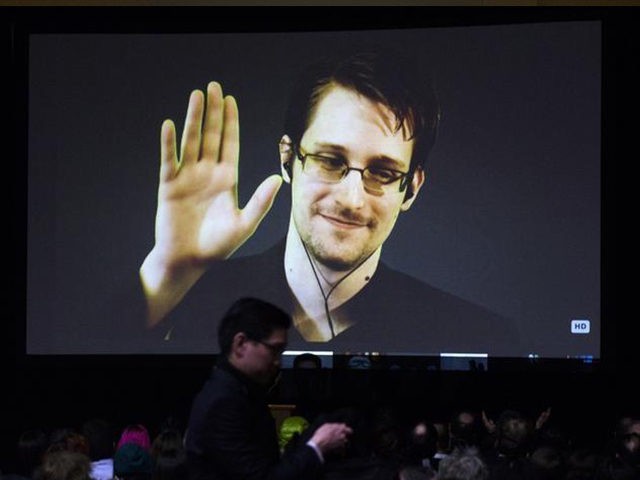
While much of the report is redacted, information related to the poor security practices of the NSA can still be found. The declassified security review was conducted following the leak of over one million NSA files by Edward Snowden between 2012 and 2013. The report states that the “NSA did not have guidance concerning key management and did not consistently secure server racks and other sensitive equipment in the data centers and machine rooms” in accordance with their “Secure-the-net” initiative. Data centers were also left unsecured as two-person access controls were not implemented at the time of the report. Similarly, two-factor authentication had not been rolled out to all high-level access users either.
The report states that far too many NSA employees had administrator privileges, meaning they could make direct changes to NSA systems without approval from higher-ups within the organization. These administrator accounts were also poorly monitored according to the report, and the number of NSA employees that were given permissions to perform data transfers had not been lowered in an attempt to secure data. In three separate NSA facilities, in Texas, Utah, and North Carolina State University, the team conducting the security audit “observed unlocked server racks and sensitive equipment,” leaving data extremely easy to access.
The declassified document further states that the “NSA did not keep accurate and detailed documentation that identified its methodology for completing each initiative,” and “did not describe how it measured the initiatives’ completeness and effectiveness.” This means that these security vulnerabilities were still present within NSA systems up until August of 2016. The NSA will reportedly take the findings of the security audit into consideration while tightening their internal security, but due to the heavily redacted nature of the declassified document, it is hard to determine what the NSA plans to do about their network security.
Lucas Nolan is a reporter for Breitbart News covering issues of free speech and online censorship. Follow him on Twitter @LucasNolan_ or email him at lnolan@breitbart.com

COMMENTS
Please let us know if you're having issues with commenting.