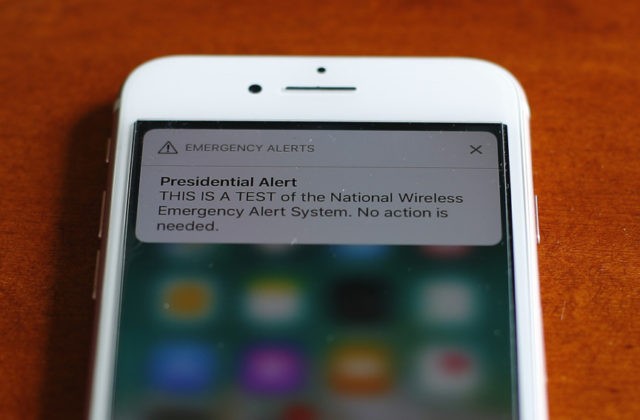
According to recent research, the U.S. emergency alert system is vulnerable to hijacking which could prove very dangerous in the hands of America’s enemies.
A report from Vice News titled “Researchers Demonstrate How U.S. Emergency Alert System Can Be Hijacked and Weaponized,” outlines how recent research shows that the U.S. emergency alert system is more vulnerable than previously believed and could be easily exploited in a dangerous manner. Vice reports that researchers began investigating the system following the false emergency alert sent in Hawaii in 2018 which claimed that a missile attack had been launched, this was not the case and the alert was caused by a clerical error but it raised interest in the system.
VICE writes:
Their full study was recently unveiled at the 2019 International Conference on Mobile Systems, Applications and Services (MobiSys) in Seoul, South Korea. It documents how spoofing the Wireless Emergency Alert (WEA) program to trick cellular users wasn’t all that difficult.
To prove it, researchers built a mini “pirate” cell tower using easily-available hardware and open source software. Using isolated RF shield boxes to mitigate any real-world harm, they then simulated attacks in the 50,000 seat Folsom Field at the University. 90 percent of the time, the researchers say they were able to pass bogus alerts on to cell phones within range.
Researchers began to attempt to hijack the emergency broadcast system and were worried by how easily they were able to do so:
The transmission of these messages from the government to the cellular tower is secure. It’s the transmission from the cellular tower to the end user that’s open to manipulation and interference, the researchers found. The vulnerability potentially impacts not just US LTE networks, but LTE networks from Europe to South Korea.
Eric Wustrow, a co-author of the study and an assistant professor in Electrical, Computer and Energy Engineering, told Motherboard such an attack would be relatively inexpensive to fund, fairly simple to conceal, and difficult to defend against in real time.
“We were able to do this attack with commercially-available software defined radios for about €880.37,” he said. “The size of our SDR is about the size of a typical wifi router.”
Anyone with access to the system could use it to cause untold panic and terror in a specific area, an extremely worrying prospect:
The potential for sowing chaos and spreading fear in confined areas like sports stadiums should be fairly obvious. 50,000 users suddenly being warned of a potential attack by nerve gas, for example, would clearly result in some obvious public safety issues.
Wustrow’s team says it has been working with governments and cellular carriers on potential mitigation measures that could help limit the attack’s effectiveness.
Read the full report by VICE here.
Lucas Nolan is a reporter for Breitbart News covering issues of free speech and online censorship. Follow him on Twitter @LucasNolan or email him at lnolan@breitbart.com

COMMENTS
Please let us know if you're having issues with commenting.