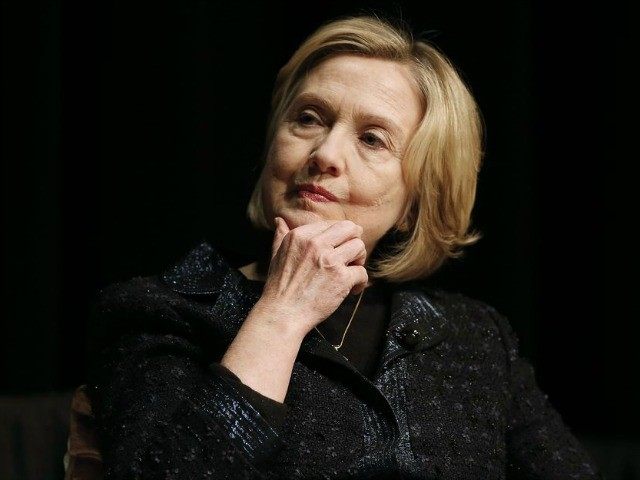
In a decision that took place while Hillary Clinton was Secretary of State, the Department’s Inspector General issued a blistering report on the behavior of the US Ambassador to Kenya which included the ambassador’s ill-advised use of private email accounts.
The IG report was highlighted on Twitter earlier today by @CuffeMeh. The IG report states in its key findings that “the Ambassador’s greatest weakness” was his reluctance to follow US-government decisions including “the nonuse of commercial email for official government business, including Sensitive But Unclassified information.” The report expands on the ambassador’s poor decision making in this regard:
Very soon after the Ambassador’s arrival in May 2011, he broadcast his lack of confidence in the information management staff. Because the information management office could not change the Department’s policy for handling Sensitive But Unclassified material, he assumed charge of the mission’s information management operations. He ordered a commercial Internet connection installed in his embassy office bathroom so he could work there on a laptop not connected to the Department email system.
Why would the ambassador want an internet connection in the bathroom? According to a report in the New Republic, published shortly after the ambassador resigned, he did it because the bathroom was “one of the few places in Embassy Nairobi authorized for an unsecured network.” He even held meetings in the bathroom (subordinates would sit on the toilet) to get around the spirit of the rules while still obeying the letter. The IG report continues [emphasis added]:
He drafted and distributed a mission policy authorizing himself and other mission personnel to use commercial email for daily communication of official government business. During the inspection, the Ambassador continued to use commercial email for official government business. The Department email system provides automatic security, record-keeping, and backup functions as required. The Ambassador’s requirements for use of commercial email in the office and his flouting of direct instructions to adhere to Department policy have placed the information management staff in a conundrum: balancing the desire to be responsive to their mission leader and the need to adhere to Department regulations and government information security standards.
The report goes on to note that the ambassador did not have his government computer hooked up to official networks. This was ill-advised for both security reasons and because it could lead to loss of records which the department is required to maintain [emphasis added]:
According to 12 FAM 544.3 and 11 State 73417 (from the Assistant Secretary for Diplomatic Security to the Ambassador), it is the Department’s general policy that normal day-to-day operations be conducted on an authorized information system, which has the proper level of security controls. The use of unauthorized information systems increases the risk for data loss, phishing, and spoofing of email accounts, as well as inadequate protections for personally identifiable information. The use of unauthorized information systems can also result in the loss of official public records as these systems do not have approved record preservation or backup functions. Conducting official business on non-Department automated information systems must be limited to only maintaining communications during emergencies.
In recommendation number 57, the IG stated plainly, “Embassy Nairobi should cease using commercial email to process Department information and use authorized Department automated information systems for conducting official business.”
Ambassador Scott Gration resigned from his position in June 2012. The IG report was apparently published in August of that year. All of it happened while Hillary Clinton was Secretary of State.

COMMENTS
Please let us know if you're having issues with commenting.