Indonesia’s Health Ministry said on Tuesday it was investigating an alleged security breach of its Chinese coronavirus contact tracing app that potentially exposed the personal identification information of more than 1.3 million users.
“Right now, we’re investigating this suspected breach,” Anas Ma’ruf, an Indonesian health ministry official, told Reuters on August 31.
A team of cybersecurity researchers from the online encryption provider vpnMentor said they discovered a data breach of the Indonesia Health Alert Card (eHAC) on July 15 and alerted Jakarta to the security gap on July 21 before publishing their findings on August 30. The Indonesian Ministry of Health uses eHAC, a smartphone app, to “test and trace” people entering the country as part of an effort to mitigate domestic transmission of the Chinese coronavirus.
“It’s a mandatory requirement for any traveler entering Indonesia from overseas, both Indonesian citizens and foreigners,” vpnMentor wrote of the eHAC app. “It’s also required for domestic flights within Indonesia.”

A health worker administers a dose of the Sinovac coronavirus vaccine at a convention hall building in Banda Aceh, Indonesia, on July 26, 2021. (Chaideer Mahyuddin/AFP via Getty Images)
The app, commonly known as a “vaccine passport,” is downloaded onto a traveler’s personal smartphone. It then stores the individual’s “health status, Personally Identifiable Information (PII) data, contact details, COVID-19 [Chinese coronavirus] test results, and much more,” according to vpnMentor.
“Our team discovered eHAC’s records with zero obstacles, due to the lack of protocols put in place by the app’s developers,” the online encryption provider stated in its report.
“The developers of eHAC were using an unsecured Elasticsearch database to store over 1.4 million records from approximately 1.3 million eHAC users,” vpnMentor revealed.
“These records didn’t just expose the users. This data leak exposed the entire infrastructure around eHAC, including private records from hospitals and Indonesian officials using the app,” according to the report.
VpnMentor warned that the security breach could expose eHAC users to online phishing or hacking attempts, identity theft, and various financial crimes. The potential for societal damage through a security breach in a government-run app is far greater, according to the online encryption provider.
“The records stored within the eHAC database could potentially allow hackers to access the app directly and change data on passengers, including their COVID-19 [Chinese coronavirus] test results,” VpnMentor wrote. “Given the scale of records exposed and the number of people being tested, such an action could wreak havoc on Indonesia’s response to the pandemic.”
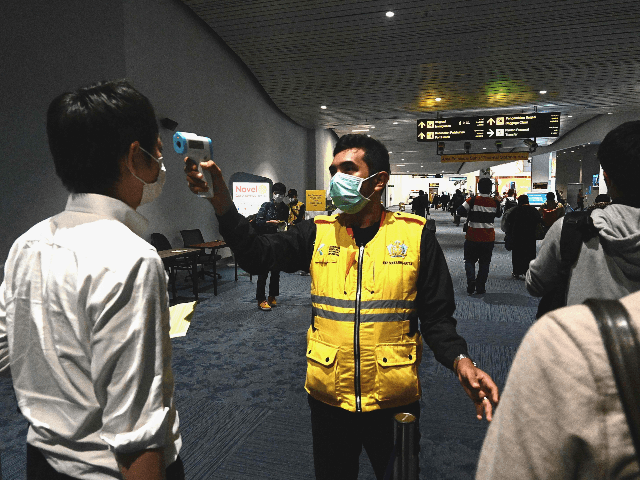
An Indonesian health official takes temperature readings of arriving passengers amid concerns of the coronavirus at the Jakarta International Airport on February 23, 2020. (Goh Chai Hin/AFP via Getty Images)
“Due to ethical concerns, we did not test this theory, but our investigation pointed to clear indicators it would be possible,” the research team noted.
“Aside from changing records on the app, hackers could also use the database to attack it with various viruses and malicious software, including ransomware – an increasingly popular tool amongst criminal cybergangs,” VpnMentor theorized.
“A single eHAC staff member clicking a dangerous link could expose the entire network and infrastructure built to support the app. Skilled hackers could even use it as a launchpad to infiltrate and attack the highest levels of Indonesia’s government,” according to the cybersecurity team.
Indonesia’s government said in May it was investigating another possible cyber security breach of its state insurer, BPJS Kesehatan, that allegedly exposed the social security data of over 100,000 people who receive universal healthcare. If true, the repeated data breaches of Indonesian government entities in recent months suggest Jakarta may suffer from underlying weaknesses within its cyber security infrastructure.


COMMENTS
Please let us know if you're having issues with commenting.