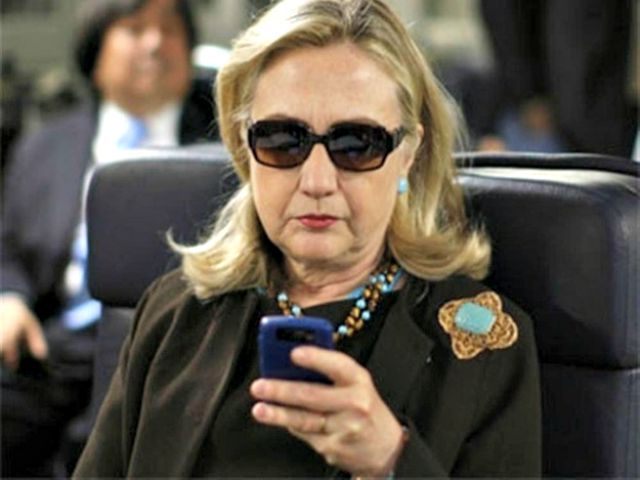
Hillary Clinton’s private email server had a webmail subdomain that made it highly vulnerable to hackers, Breitbart News has learned.
clintonemail.com had a subdomain called webmail.clintonemail.com, according to the account’s GoDaddy.com encryption certificate. That subdomain is a web-based email portal that considerably weakened the server’s defenses and invited attack.
A webmail portal allows web traffic to bypass hardware and software firewalls to easily access the server’s mail “interface.”
If a user accesses emails through a web portal on an unsecure network like Clinton’s, then the emails can be read without any encryption whatsoever for safety.
The webmail portal vastly increased the chances that Clinton’s server was hacked, a computer expert tells Breitbart News. Some hacking engines specifically target webmail portals like the one Clinton had, looking for access to email accounts.
And since hers was a web-based portal, Clinton’s few lines of defense for her server – including a spam-filtering system called MXLogic and a company in Florida that kept perfunctory tabs on the account – probably would not have even known if a hack occurred.
Additionally, Clinton’s server’s encryption was a Sha1 encryption combined with an RSA encryption. That encryption is very weak. Sha1 without an RSA encryption to compliment it is so weak and prone to hacks that it has been getting phased out of use for about a decade. Even the added RSA encryption does not negate the vulnerability to hacks of Clinton’s Sha1 encryption.
Sha1 is about 64,000 times less secure than the encryption for the extramarital dating website Ashley Madison, which was recently hacked, exposing the personal information of all of the site’s users.
“Due to [Ashley Madison] employing these methods one of the specialists attempting to reveal the true passwords was limited to 156 guesses per second instead of the 7m-11m that would be possible with more common, weaker methods of hashing such as MD5 or SHA1,” according to a posting on a tech forum.
COMMENTS
Please let us know if you're having issues with commenting.