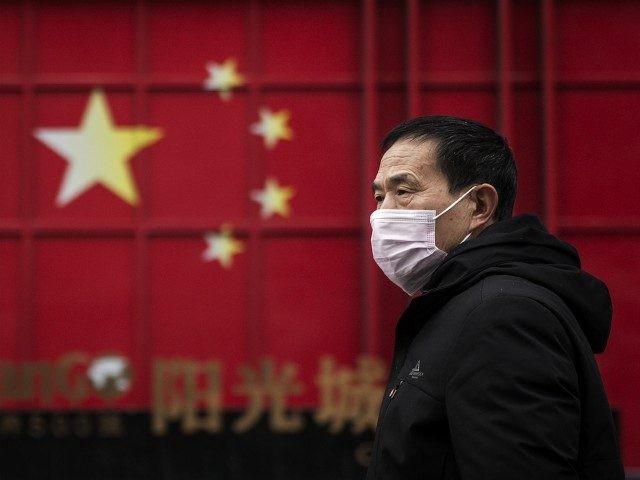
According to a recent report, video conferencing app Zoom has admitted that some Zoom video conferencing calls were routed through China. According to the researchers that discovered the routing problem, Chinese authorities could demand that Zoom turn over any encryption keys on its servers in China in order to decrypt the contents of video calls.
TechCrunch reports that the video conferencing app Zoom has admitted that some Zoom calls were routed through China just hours after a report on the issue from security researchers at Citizen Lab.
Breitbart News recently reported that the CEO of the video conferencing company has apologized in a blog post over the various security issues that its 200 million daily users are facing on the platform. CEO Eric Yuan announced a number of measures that the company is taking to make the app more secure as millions of Americans use the app to work and study from home. Breitbart News covered the criticism of the company over its lack of action on “Zoom bombing” this week.
Zoom’s usage has exploded since the beginning of the coronavirus pandemic in January as many worldwide are forced to work or attend school from home, using the app for group meetings and online classes. In the blog post, Yuan stated that usage had increased by 1,900 percent with 200 million daily free and paying users in March up from 10 million at the end of December.
However, as Breitbart News has reported, the increased usage has also attracted online hackers and trolls. Hijacking zoom meetings to disrupt business and schoolwork has gained the nickname “Zoom bombing” on the Internet.
Now, according to a report from Citizen Lab researchers, some calls made via Zoom in North America were routed through China as were the encryption keys used to secure those calls. Zoom said in a recent blog post that it has “implemented robust and validated internal controls to prevent unauthorized access to any content that users share during meetings.” However, Chinese authorities could easily demand that Zoom turn over any encryption keys on its servers in China in order to decrypt the contents of encrypted calls.
Zoom now states that it has increased efforts to improve its server capacity to accommodate the huge increase in users in recent weeks. Zoom CEO Eric Yuan stated:
During normal operations, Zoom clients attempt to connect to a series of primary datacenters in or near a user’s region, and if those multiple connection attempts fail due to network congestion or other issues, clients will reach out to two secondary datacenters off of a list of several secondary datacenters as a potential backup bridge to the Zoom platform. In all instances, Zoom clients are provided with a list of datacenters appropriate to their region. This system is critical to Zoom’s trademark reliability, particularly during times of massive internet stress.”
Citizen Lab researcher Bill Marczak told TechCrunch that he was “cautiously optimistic” about Zoom’s response.
“The bigger issue here is that Zoom has apparently written their own scheme for encrypting and securing calls,” he said, and that “there are Zoom servers in Beijing that have access to the meeting encryption keys.”
“If you’re a well-resourced entity, obtaining a copy of the Internet traffic containing some particularly high-value encrypted Zoom call is perhaps not that hard,” said Marcak.
“The huge shift to platforms like Zoom during the COVID-19 pandemic makes platforms like Zoom attractive targets for many different types of intelligence agencies, not just China,” he said. “Fortunately, the company has (so far) hit all the right notes in responding to this new wave of scrutiny from security researchers, and have committed themselves to make improvements in their app.”
Read the Citizen Labs report here.
Lucas Nolan is a reporter for Breitbart News covering issues of free speech and online censorship. Follow him on Twitter @LucasNolan or contact via secure email at the address lucasnolan@protonmail.com

COMMENTS
Please let us know if you're having issues with commenting.