Bass Suing Trump over Migrant Raids
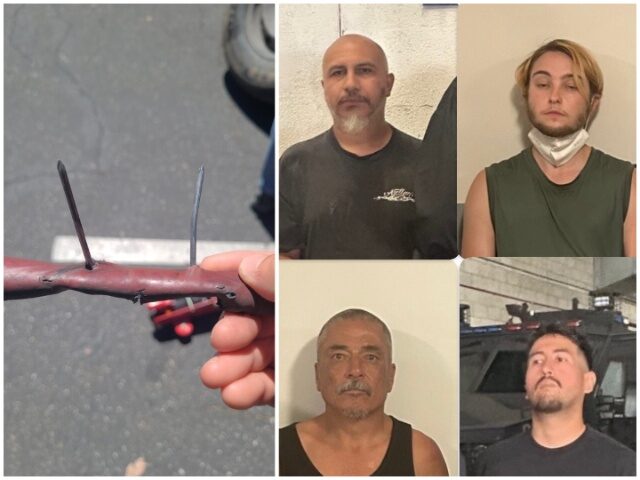
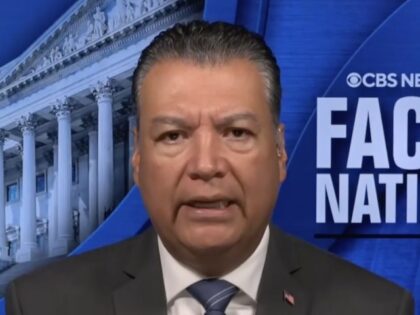
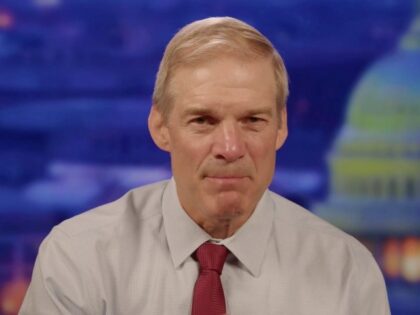
Cali vs ICE Escalates

Los Angeles Mayor Karen Bass announced Tuesday that the city will be joining a private class action civil lawsuit against the Trump administration over Immigration and Customs Enforcement (ICE) raids.