Golden Age Secured: House Passes BBB
Strongest Legislation Ever for Workers, Families
Border Security, Blocks Tax Hike
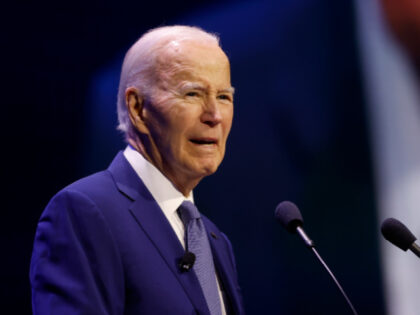
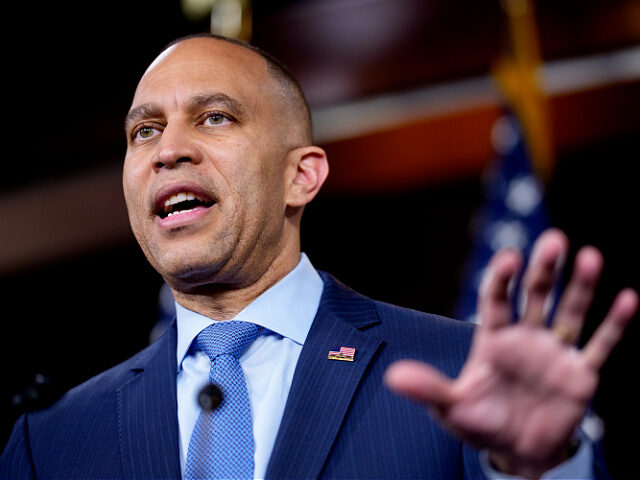
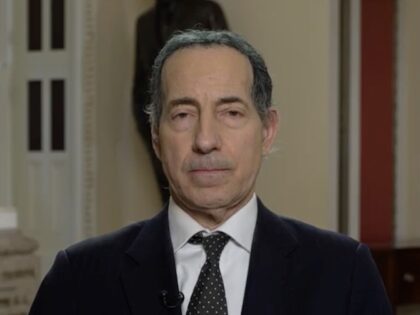
Democrat Meltdown of the Ages!
🇺🇸Signing on 4th of July🎉
Historic Trump Victory

President Donald Trump’s big, beautiful bill is en route to the White House, the culmination of months of work by the President and his team and the realization of scores of campaign promises.